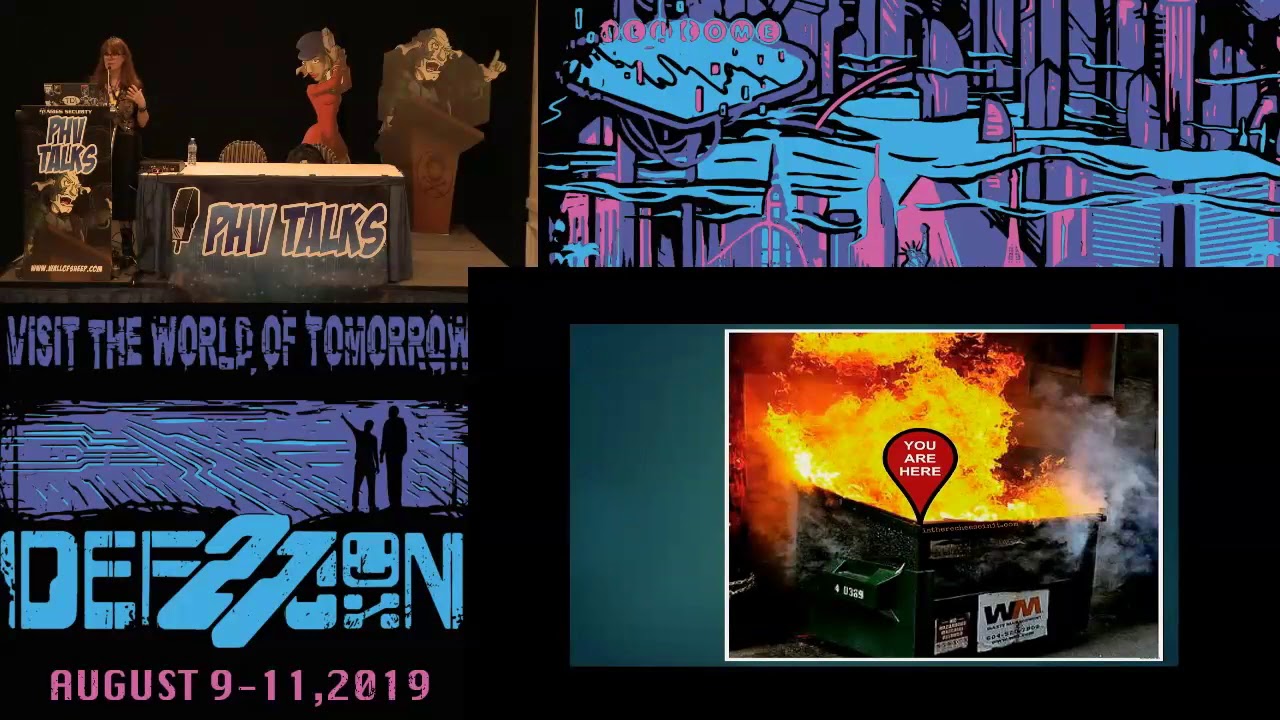
Cheryl Biswas — Patching It is Complicated — DEF CON 27 Packet Hacking Village
Patching – it’s complicated. Organizations at every level struggle with security updates in a fundamental process that seems more like a necessary evil than a best practice. The fact is, one size does not fit all when security patches get issued and things can go very wrong. What actually determines enterprise patching cycles? How should we prepare for the pernicious spread of unpatched BYOD that gets connected? We need to go beyond just finding the sweet spot between mitigating business risk with vulnerability exposure. Because the cure isn’t supposed to be worse than the disease.
Cheryl Biswas (Twitter: @3ncr1pt3d) is a Strategic Threat Intel Analyst with a major bank in Toronto, Canada. Previously, she was a Cyber Security Consultant with KPMG and worked on security audits and assessment, privacy, breaches, and DRP. Her experience includes project management, vendor management and change management. Cheryl holds an ITIL certification and a degree in Political Science. Her areas of interest include APTs, mainframes, ransomware, ICS SCADA, and building threat intel. She actively shares her passion for security online, as a speaker and a volunteer at conferences, and by encouraging women and diversity in Infosec as a founder and member of the «The Diana Initiative».